Emergency Access Management for SAP (EAM)
That's what it's all about
Any direct access to the SAP production systems with superuser permissions represents a high risk. Fraud and unintended activities may result in financial loss or incorrect financial reporting with potential serious consequences. That is why they are under particular observation from auditors and tax authorities.
Best practices
A good emergency user concept assures that,
a documented emergency access concept exists
the Superuser credentials are secured against unauthorized access
every Superuser deployments are logged
any use of emergency user credentials is subject to an approval and notification process
The review of every Emergency User operations is mandatory and documented
A specialized software is crucial
The traceability of each and every Emergency User operation with SAP standard functionalities is almost impossible (audit trail). This comprises the assignment of Superuser credentials itself, the protocoling of any actions (Security Audit Log) during the emergency access and ends with the review of all log files. When you have multiple instances and distributed clients, the centralized monitoring and reporting is also challenging. And, at the end you need to provide internal end external auditors with evidences.
A revolutionary concept – ISPICIO_E
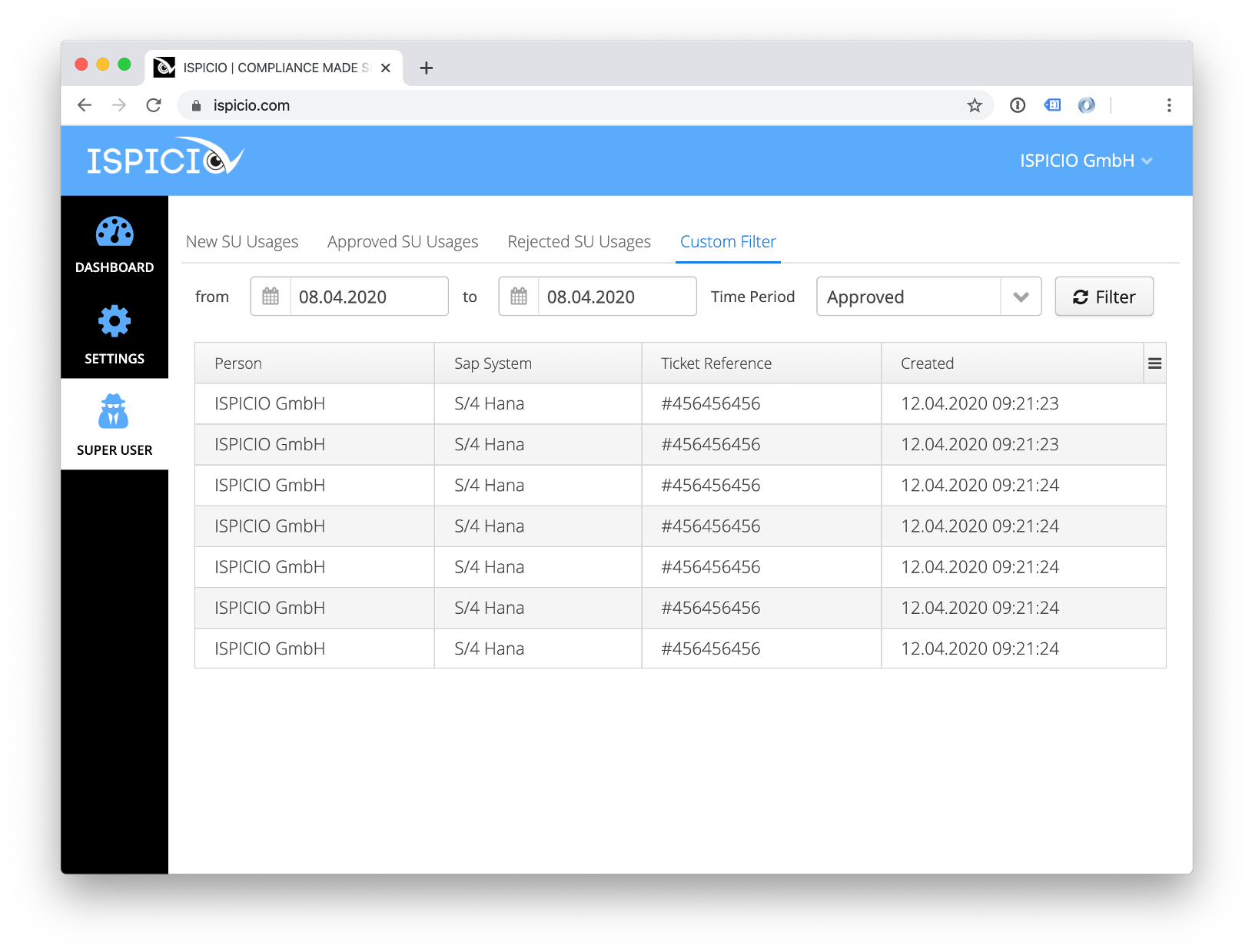
We came up with an unusual approach: Our Emergency Access Management software (EAM) is based on a web server application and connects to SAP via RFC. To start an emergency access, entitled users browse to ISPICIO_E (Intranet) and log-in with their individual credentials. Here they enter a reason and a ticket reference ID. After doing so, they obtain an one-time Superuser ID. In the background, ISPICIO_E creates a dedicated Emergency User and links it to the Security Audit Log (SAL). Then, ISPICIO_E checks continuously if the Superuser is still active. If not, ISPICIO_E deletes this particular Superuser again and downloads the SAL log file to the internal database. In the aftermath, a mandatory review of the Security Audit Log file is assigned to a reviewer for approval, which is documented, too.
Key Benefits
Our approach meets all the requirements for a compliant management of SAP Emergency Users and has many advantages:
Installation and setup is straightforward: Rapid implementation, no specialists, no training is needed
an unlimited number of SAP systems can be connected, regardless of their location and without additional license costs
each and every emergency user incident, its protocols and reviews are stored centrally for monitoring, reporting and auditing
Best of all: ISPICIO_E is reasonably priced